1. What is Code42?
 Code42 is a Software-as-A-Service cybercrime prevention tool. The company was founded in 2001 by Matthew Dornquast, Brian Bispala and Mitch Coopet, with Dornquast serving as the CEO until 2015. Code42 is based in Minneapolis, U.S. The software’s primary solutions are Insider risk, data exfiltration and incident response.Over 50,000 organizations use Code42, including CrowdStrike, MacDonald Miller, MACOM and Snowflake. Code42 offers an interactive demo in their own sandbox environment, along with a 30-day free trial. You can reach out to the sales team for pricing plans,and their insider risk consultant will advise you. For small businesses,Code42’s CrashPlan Pro edition will be suitable, and costs USD 10 per month per computer.
Code42 is a Software-as-A-Service cybercrime prevention tool. The company was founded in 2001 by Matthew Dornquast, Brian Bispala and Mitch Coopet, with Dornquast serving as the CEO until 2015. Code42 is based in Minneapolis, U.S. The software’s primary solutions are Insider risk, data exfiltration and incident response.Over 50,000 organizations use Code42, including CrowdStrike, MacDonald Miller, MACOM and Snowflake. Code42 offers an interactive demo in their own sandbox environment, along with a 30-day free trial. You can reach out to the sales team for pricing plans,and their insider risk consultant will advise you. For small businesses,Code42’s CrashPlan Pro edition will be suitable, and costs USD 10 per month per computer.2. Code42 and CrashPlan-Features in Detail
 Incydr Code42’s risk detection platform enables security teams to resolve risks arising from exposed files without interrupting existing flows of work. Incydr monitors data, vectors and users. We’ll go into what these are;
Incydr Code42’s risk detection platform enables security teams to resolve risks arising from exposed files without interrupting existing flows of work. Incydr monitors data, vectors and users. We’ll go into what these are;Data
Data refers to all files. It looks into file name, owner, size, path, location and category and gives cybersecurity analysts visibility to review file content.Vector
Incydr detects exfiltration such as uploads and syncing activities on the web and cloud. It also monitors file shares, and insertion and removal of media from systems. The logs include domain name, browser tab title, make of media, partition ID and serial number. It filters events and categorizes them as trusted or untrustworthy activity.User
Incydr identifies risky behaviors on the abscess of remote activity, offline file events and concealment attempts. In doing so,security teams can monitor user and usage and block suspicious activity. You can analyze trends through 90-day historical data and identify abnormal deviations.
2.1 Detection
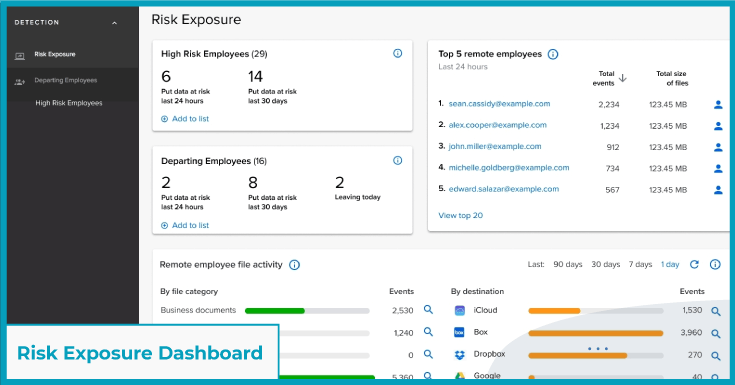
Risk Exposure Dashboard
The risk exposure dashboard gives the company a bird’s eye-view of suspicious data sharing, exfiltration and performance concerns according to the file type, employee profile and vector. It lets you see a list of employees whose records indicate suspicious behavior. It also includes risk factors such as the type of employee contract(whether contractual, full-time or casual, flight risks, access rights and performance concerns.
How it benefits companies
Labeling risky activities enables you to recognize and respond to them in-time. It shows security gaps, and informs you of policy violations. The risk exposure dashboard identifies active-times per employee, i.e. the length of time an employee is online and active on their device to create a pattern from start to finish. This makes it easier to pick up activities if they take place outside these hours. Incydr uses IP addresses to determine off-network activities that raise risks.
High-fidelity alerts
The alerts can be mailed or sent to an operational system of record and are triggered based on preset criteria. This includes emailing or uploading files to unsafe domains and URLS. The alerts notify you of activities that are abnormal, which contextualizes insider risk investigations.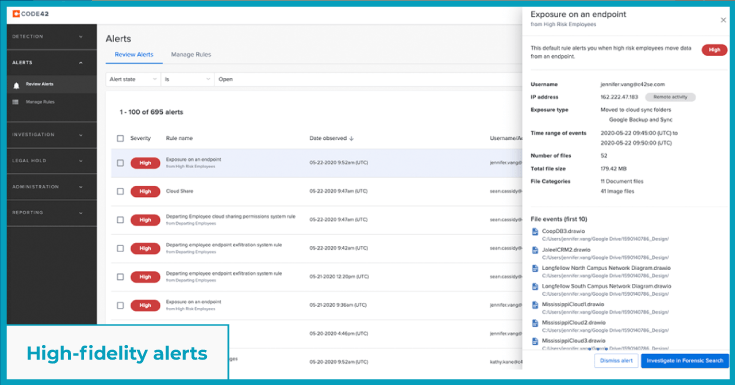 How it benefits companies Alerts enable companies to identify times that an employee puts data concerning the business at a higher risk, such as at the time of resignation. Security experts can set thresholds for acceptable activity to receive quicker and specific alerts
How it benefits companies Alerts enable companies to identify times that an employee puts data concerning the business at a higher risk, such as at the time of resignation. Security experts can set thresholds for acceptable activity to receive quicker and specific alertsRisk Exposure Lenses
The risk exposure lens kicks off system alerts, user management profiles and enables you to protect vulnerabilities. It takes user attributes such as user name, ID, contract type and department from the company’s employee database and groups risks by employee behavior.How it benefits companies
The lens establishes context in terms of where and when breaches are caused and who is causing them. It enables you to recognize a pattern and categorize all known and even unknown risks, thereby ensuring you’re always a step ahead.
2.2 Investigation
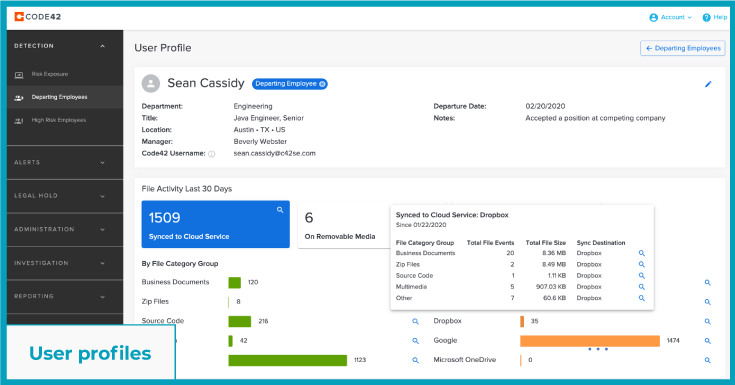
User profiles
User profiles let you view any staff’s computer and cloud activity for upto 90 days. You can review the data in context of the employee’s name and departmental manager they report to. Any off-hour file events can be prioritized for investigation.
How it benefits companies
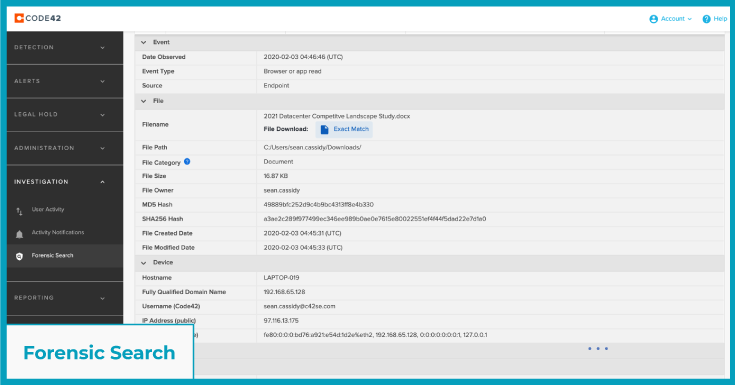
User profiles help security teams review device metadata against the username of the person logging into the device. It also includes the IP addresses (both private and public). You can search instances of a particular activity, recurrences, trends and abnormalities.Forensic Search
The forensic search feature indexes file events over a 90-day period, regardless of your device being on or off. The search parameters are pre populated based on the activities detected via fidelity alerts, risk response dashboards and user profiles.
How it benefits companies
Forensic searches aid in auditing and reconciliation. It enables you to review the type and source of exposure in order to know the activity that set it off. Files. You can perform an exploratory analysis by searching for the file hash to know who last accessed files, and to reconfirm if employees were authorized to.Security information and event management
Incydr’s data exfiltration and alerts feed information to your security information and event management (SIEM) system for faster risk assessment. It integrates with applications like Exabeam, Splunk and Sumologic.How it benefits companies
Incydr keeps your SIEM up-to-date by running routine deep-scans. It draws from data ported from other tools and applications that are integrated into the platform. .
2.3 Response
Cases
The case feature within Incydr response compiles, documents and disseminates event investigation details to the security panel for them to fast-track mitigative measures.How it benefits companies
The case feature escalates insider risk incidents to the employee’s manager, legal panel or human resources department for further action.Automated Response
The insider risk playbook helps close incidents quickly and at-scale. It sends out automated alerts to your platform to investigate activities across endpoints and users, including those employees who are about to leave the firm or belong to a business unit closing down.How it benefits companies
Automated alerts trigger warnings that you can prioritize and customize by your organization’s needs.Outreach remediation
Incydr lets you confront employees with the evidence of wrongdoing and resolve conflicts of interest internally. This helps you help the employee to understand what the risk is and to reiterate company policies regarding the exchange and trafficking of data.How it benefits companies
Remediation helps you improve the quality of security awareness training. It enables businesses to handle risk responses without going to extreme measures.File Recovery
Incydr can recover files, including older versions and deleted files. Authorized security users can restore or download files to original destinations and devices. Even intentional deletions can be reversed to ensure your file can be recovered.How it benefits companies
If a user deletes files on purpose to cover up their tracks, this feature can undo the action and ensure the company stays in control of the access, retrieval and distribution of content.
3. Incident Response
Incident response is a structured method for detecting, responding to and mitigating security breaches. Within Code42, the incident response feature prevents high-impact data leaks which include accidental customer information leaks, surreptitious file thefts, file exposure from cloud storage and drives, IP theft, corporate espionage and tampering of files.We found that the security applications with which Code42 integrates itself into enables it to deploy an agent to monitor all file activity on multiple platforms. It alerts corporations of removable media in-use and runs rules for checking if files being shared fall under legal or unauthorized activity.4. Insider Risk
Insider Risk refers to confidential data being exposed that compromises company, trade,customer, and employee information. Incydr’s insider risk feature can filter out activities such as harmless file sharing between two trusted devices and networks, while identifying and revealing risky or inexplicable blips that you need to take a second look at. Insider risk combines content from files, vectors and users to prioritize events that need to be investigated.5. Data Exfiltration
Incydr’s exfiltration detection works by monitoring high-risk activities such as browser and web uploads, email attachments, flash drive file transfers and message retrieval on collaboration platforms such as Slack, Dropbox and iCloud. It identifies employees by their ID and activity to classify who among them are the most likely to risk data security. Managers can accordingly order investigation into such activities, and institute security awareness training strategies.6. What is CrashPlan Cloud?
CrashPlan is a file-watching tool designed to backup laptops and desktops. It restores files to their original or new location, and facilitates file recovery remotely or through self-service. This enables you to manage a legal hold on company policies to preserve and secure files.7. Ease of Use-The SorryIWasOnMute Verdict
 The team and I felt Incydr’s risk response dashboard was filled with information vital to recognizing, responding to, and resolving issues perceived as threats. More importantly, you can see where it's coming from and won’t be blindsided when there’s suspicious activity.Once you land on the dashboard, it's easy to see activities and map it by the timestamp of access and who accessed it. Incydr’s trial allowed us to test out CrashPlan too, which scans files, migrates data and backs up devices so that you’re assured of never losing any business data permanently.
The team and I felt Incydr’s risk response dashboard was filled with information vital to recognizing, responding to, and resolving issues perceived as threats. More importantly, you can see where it's coming from and won’t be blindsided when there’s suspicious activity.Once you land on the dashboard, it's easy to see activities and map it by the timestamp of access and who accessed it. Incydr’s trial allowed us to test out CrashPlan too, which scans files, migrates data and backs up devices so that you’re assured of never losing any business data permanently.8. Pros and Cons of Code42
 Code42’s Incydr platform is a robust security monitoring system that enables businesses to stay on top of risks and mitigate them before it's too late. A few pros we spotted from our brief time on the tool included;
Code42’s Incydr platform is a robust security monitoring system that enables businesses to stay on top of risks and mitigate them before it's too late. A few pros we spotted from our brief time on the tool included;- Risk labeling, which lets you profile the severity of the risk by where it's coming from, and mapping it to a user activity.
- Remediation and file recovery, which is weaved into the tool’s capability. Self-healing, which refers to identifying bad blocks of data that are archived and restored only after threats are sealed off.
- The rule-based alerts make sure that your day isn’t being interrupted by a dozen alerts. You only get notifications for flagged activities and deviations from fed-in patterns, such as a user logging in and accessing files during off-work hours.
9. What SorryIWasOnMute Thinks
 Before the team and I got into the Code42 review, we did think that it came off sounding like the tool was helping you look for an excuse to confront an employee. As we continued to use it to understand how the features work, we came to realize that the Code42 helps both employees and employers understand what actions are risky and compromise the safety of personal and professional data.For this reason, we rate Incydr Code42 an 8 on 10. Data is the new oil, and so long as data lies within our control, businesses must do everything to recognize the type and likelihood of risks, recurrences, triggers and roll out appropriate measures to preempt it.Following this Code42 review, which tool would you like us to review next?
Before the team and I got into the Code42 review, we did think that it came off sounding like the tool was helping you look for an excuse to confront an employee. As we continued to use it to understand how the features work, we came to realize that the Code42 helps both employees and employers understand what actions are risky and compromise the safety of personal and professional data.For this reason, we rate Incydr Code42 an 8 on 10. Data is the new oil, and so long as data lies within our control, businesses must do everything to recognize the type and likelihood of risks, recurrences, triggers and roll out appropriate measures to preempt it.Following this Code42 review, which tool would you like us to review next?